Eliminate Email Cyber Threats
Total inbox control and email security.
Email security options for every situation.
Reclaim your email—and your productivity.
The challenges of email security are growing every day. New threats from ransomware and phishing attacks are appearing with increasing frequency.
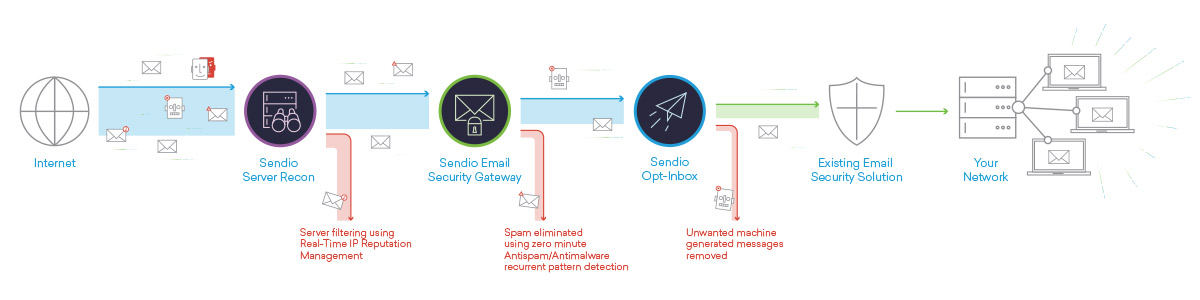
Sendio eliminates the threat posed by malicious email and eradicates productivity lost to an avalanche of spam.
With Sendio’s ease of deployment and use, your email security will once again be completely under your control—regardless of whether you deploy Sendio as the full solution or add our products to your existing system.
The Sendio solution is a clever and ingenious product that tremendously inconveniences the spammers.
SECURITY CUSTOMER
[Sendio] is an effective anti spam system that is easy to implement and it is both user & system administrator friendly. It gives users control of their inbox and visibility of their e-mail flow.
CONSUMER PACKAGED GOODS CUSTOMER
Over the years, I have used several methods for protecting my end users from spam, but I have never used a product as simple and effective as Sendio.
COMPUTER CONSULTANT CUSTOMER
[Sendio] has completely eliminated our spam problem – effortlessly – and freed up numerous hours each day, leading to better employee productivity.
